Welcome to the third article about how to create your own Template with Microsoft Threat Modeling Tool 2016.
The first article of the series, where I introduced how to create your own Template, can be found in Threat Modeling Templates: how to start your own. The second article, dedicated on the definition of your own Entities, can be found in Threat Modeling Templates: the Stencils.
This new article discusses the second Tab in the Template Editor, which is dedicated to creating and modifying the various threats that are generated by the tool based on the model.
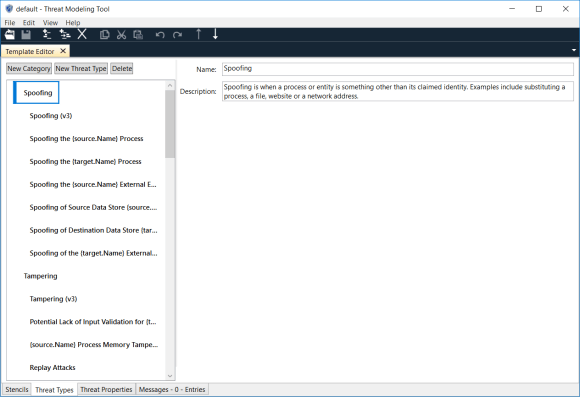
The Threat Types tab contains a two-levels tree, where the first level represents the Threat Category and the second level represents the Threat Type.
The Threat Category represents a simple way to collect the Threats based on their type. The default template shipped with the Microsoft Threat Modeling Tool adopts the STRIDE classification of Threats. STRIDE is an acronym for Spoofing, Tampering, Repudiability, Information Disclosure, Denial Of Services and Elevation of Privilege. STRIDE has been defined by Microsoft to simplify the identification of the Threats and their mitigation. This is not necessarily the only possible categorization: for example, CAPEC by MITRE categorizes the Threats based on the Mechanism of Attack or the Domain of the Attack, that is Social Engineering, Supply Chain, Communications, Software, Physical Security and Hardware.
Under the Threat Categories, you have the Threat Types, which represent the definitions of the Threats that will be generated by the Threat Modeling Tool 2016.
Each Threat Type is defined by a Title, which can bee created dynamically based on the entities related to the Threat. Remember that Threats in Threat Modeling Tool 2016 are associated to the flows: this means that Threats are associated to the Flow, to its Source, its destination (better known as Target) and finally to the presence of a Trust Boundary crossing the flow. This means that you can use the properties of those entities to compose dynamically the Title. An example is in the image below: the “Spoofing the {source.Name} Process” would become “Spoofing the Front End Process” if the entity starting the flow is called “Front End”.
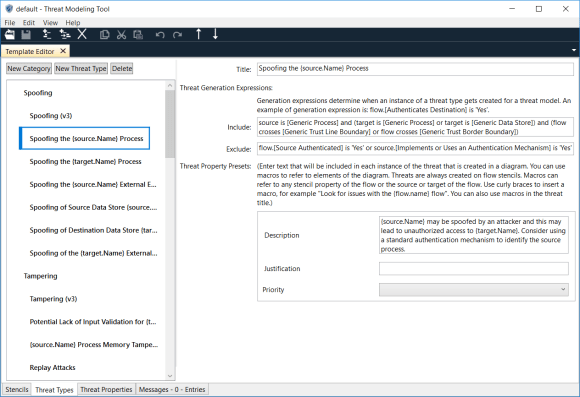
Two very important attributes of the Threat Type are the Include and Exclude Threat Modeling Expressions. In short, they represent the rules used by the Threat Modeling Tool to decide if the Threat applies to the Flow: it evaluates the Include rule first and, if it is true, it verifies the Exclude rule; if the latter is false, then the Threat is applied.
The Template Editor provides a composition editor, which helps generating the Threat Generation Expressions.
All the properties of the Entities could be used to write the Expressions.
There are also other properties: they are defined in the Threat Properties tab: we will discuss how you can define them in the next article. In the Threat Types tab, you can define the initial values for those properties for each Threat Type.
That’s all for now!





